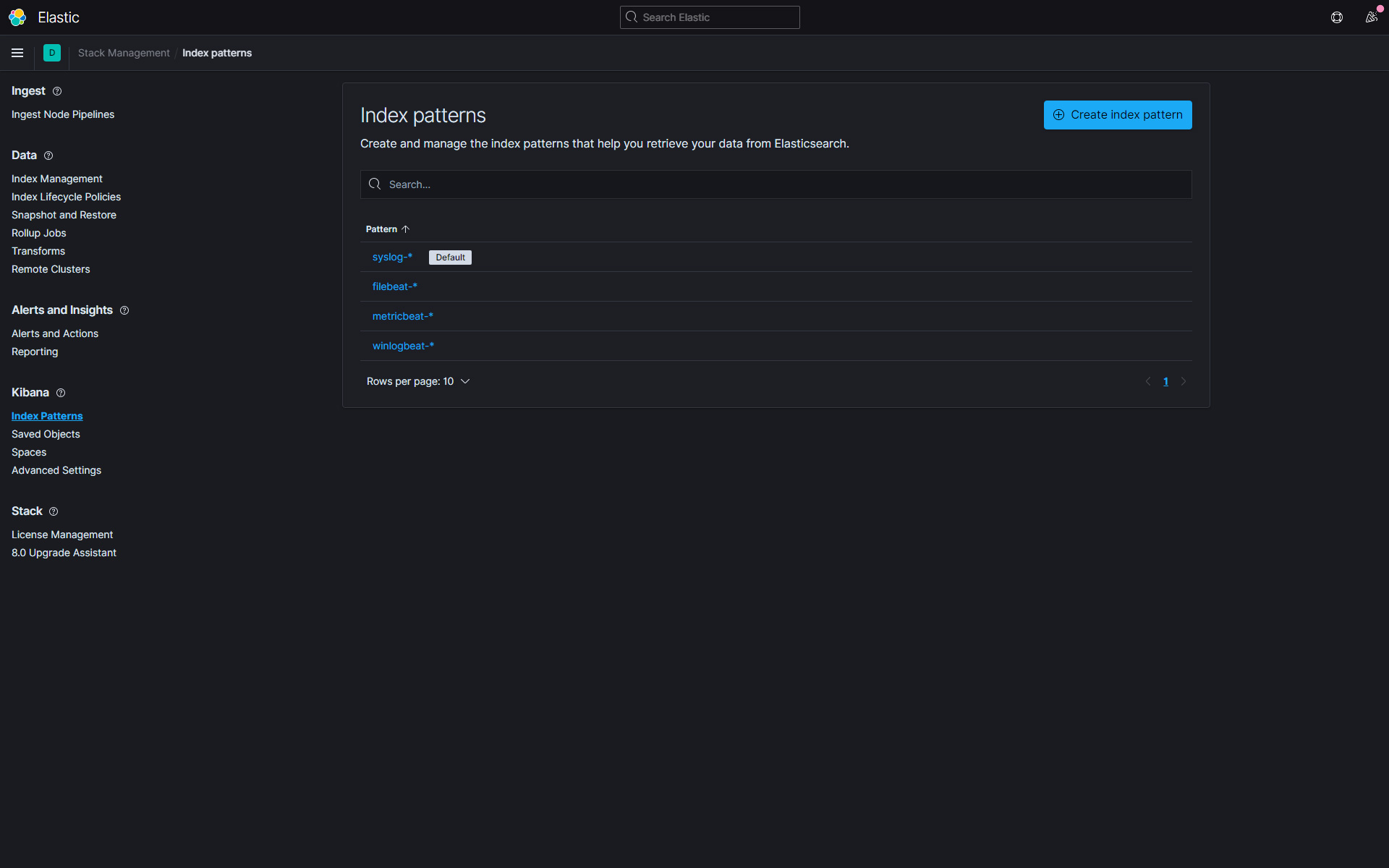
Simple example to receive log files from syslog and beats in elasticsearch using logstash
vi /etc/logstash/conf.d/multisample.conf
input {
beats {
port => 5044
tags => "beats"
ssl => false
}
udp {
port => 5055
tags => "syslog"
type => "syslog"
}
}
filter {
if [type] == "syslog" {
grok {
match => { "message" => "%{SYSLOGTIMESTAMP:syslog_timestamp} %{SYSLOGHOST:syslog_hostname} %{DATA:syslog_application}(?:\[%{POSINT:syslog_pid}\])?: %{GREEDYDATA:syslog_message}" }
add_field => [ "received_from", "%{host}" ]
}
date {
match => [ "syslog_timestamp", "MMM d HH:mm:ss.SSS", "MMM dd HH:mm:ss.SSS" ]
}
}
}
output {
if "beats" in [tags] {
elasticsearch {
hosts => ["localhost:9200"]
manage_template => false
index => "%{[@metadata][beat]}-%{[@metadata][version]}-%{+YYYY.MM.dd}"
}
}
else if "syslog" in [tags] {
elasticsearch {
hosts => ["localhost:9200"]
manage_template => false
index => "syslog-%{+YYYY.MM.dd}"
}
}
}