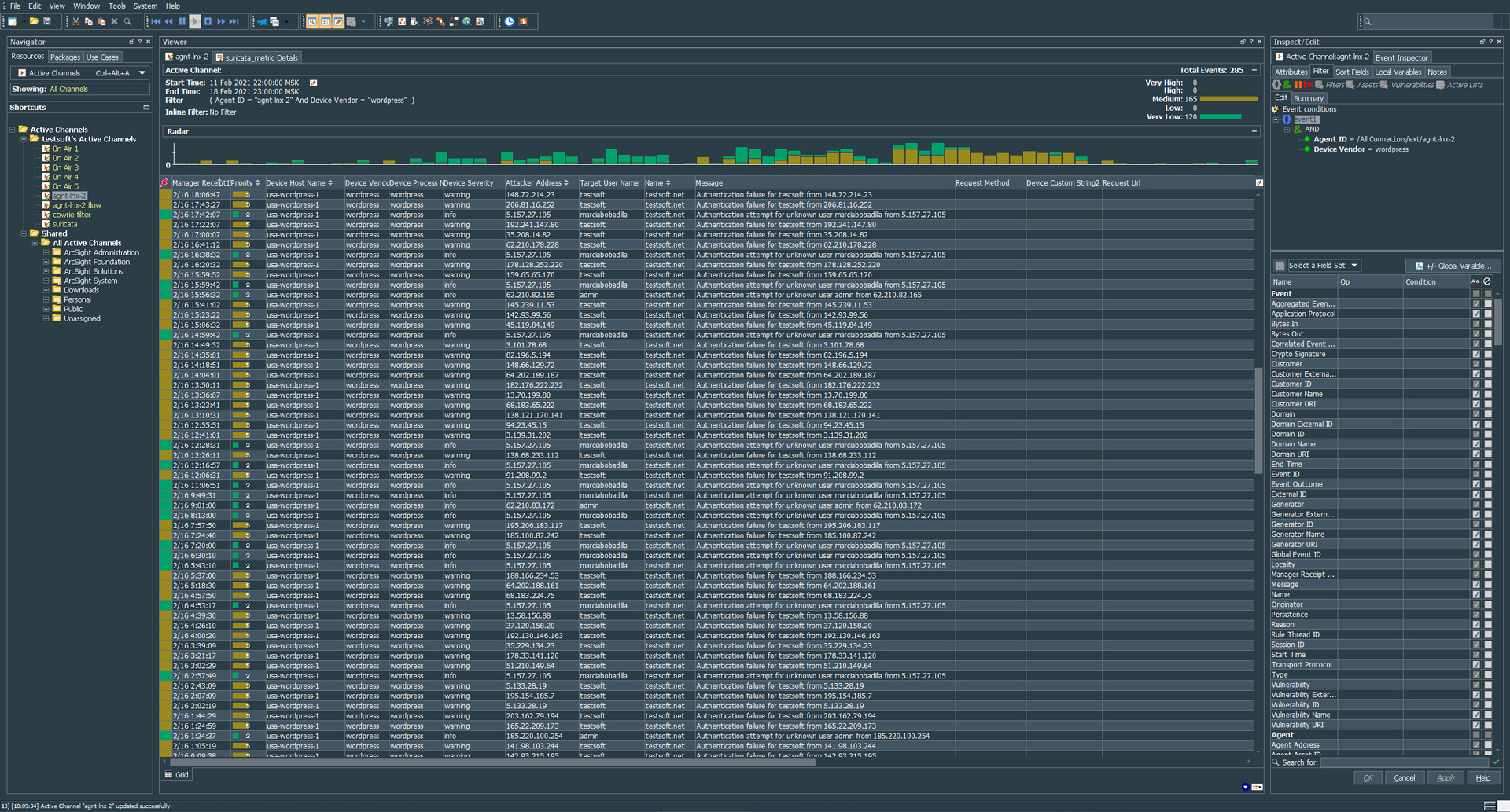
##################### # ### TESTSOFT.NET ### # ############################
### ArcSight Parser For WordPress Stock Logformat v1.0 ###
#wordpress(testsoft.net)[3673]: Authentication attempt for unknown user admin from 1.1.1.1
regex=(wordpress)(.*)
token.count=2
token[0].name=type
token[0].type=String
token[1].name=body
token[1].type=String
event.deviceVendor=__stringConstant("wordpress")
event.deviceProduct=__stringConstant("applog")
event.sourceUserPrivileges=__stringConstant("wordpress")
event.deviceProcessName=__stringConstant("wordpress")
event.flexString2=body
event.flexString2Label=__stringConstant("raw")
event.name=type
event.message=body
submessage.messageid.token=type
submessage.token=body
submessage.count=1
submessage[0].messageid=wordpress
submessage[0].pattern.count=4
#(testsoft.net)[3673]: Authentication failure for testsoft from 1.1.1.1
submessage[0].pattern[0].regex=\\(([^)]+)\\)\\[([^]]+)\\]\\:\\s+(.*failure\\s+for\\s+([^\\s+]+)\\s+from\\s+(\\d+.\\d+.\\d+.\\d+).*)
submessage[0].pattern[0].mappings=$1|$2|$3|$4|$5
submessage[0].pattern[0].fields=event.name,event.deviceCustomString4,event.message,event.targetUserName,event.attackerAddress
submessage[0].pattern[0].extramappings=event.deviceCustomString4Label=__stringConstant("pid")|event.deviceSeverity=__stringConstant("warning")
#$1 - event.name -
#$2 - event.deviceCustomString4 - pid
#$3 - event.message -
#$4 - event.targetUserName -
#$5 - event.attackerAddress -
#(testsoft.net)[3673]: Authentication attempt for unknown user admin from 1.1.1.1
submessage[0].pattern[1].regex=\\(([^)]+)\\)\\[([^]]+)\\]\\:\\s+(.*unknown\\s+user\\s+([^\\s+]+)\\s+from\\s+(\\d+.\\d+.\\d+.\\d+))
submessage[0].pattern[1].mappings=$1|$2|$3|$4|$5
submessage[0].pattern[1].fields=event.name,event.deviceCustomString4,event.message,event.targetUserName,event.attackerAddress
submessage[0].pattern[1].extramappings=event.deviceCustomString4Label=__stringConstant("pid")|event.deviceSeverity=__stringConstant("info")
#$1 - event.name -
#$2 - event.deviceCustomString4 - pid
#$3 - event.message -
#$4 - event.targetUserName -
#$5 - event.attackerAddress -
#(testsoft.net)[3673]: Accepted password for testsoft from 1.1.1.1
submessage[0].pattern[2].regex=\\(([^)]+)\\)\\[([^]]+)\\]\\:\\s+(.*Accepted\\s+password\\s+for\\s+([^\\s+]+)\\s+from\\s+(\\d+.\\d+.\\d+.\\d+))
submessage[0].pattern[2].mappings=$1|$2|$3|$4|$5
submessage[0].pattern[2].fields=event.name,event.deviceCustomString4,event.message,event.targetUserName,event.attackerAddress
submessage[0].pattern[2].extramappings=event.deviceCustomString4Label=__stringConstant("pid")|event.deviceSeverity=__stringConstant("info")
#$1 - event.name -
#$2 - event.deviceCustomString4 - pid
#$3 - event.message -
#$4 - event.targetUserName -
#$5 - event.attackerAddress -
#(testsoft.net)[3673]: Authentication attempt for unknown user admin from 1.1.1.1
submessage[0].pattern[3].regex=\\(([^)]+)\\)\\[([^]]+)\\]\\:\\s+(.*)
submessage[0].pattern[3].mappings=$1|$2|$3
submessage[0].pattern[3].fields=event.name,event.deviceCustomString4,event.message
submessage[0].pattern[3].extramappings=event.deviceCustomString4Label=__stringConstant("pid")|event.deviceSeverity=__stringConstant("info")
#$1 - event.name -
#$2 - event.deviceCustomString4 - pid
#$3 - event.message -
submessage[1].pattern.count=1
submessage[1].pattern[0].regex=(.*)
submessage[1].pattern[0].fields=event.message
submessage[1].pattern[0].extramappings=event.reason=__stringConstant("unparsed")
Arcsight flexConnector for WordPress
Posted on